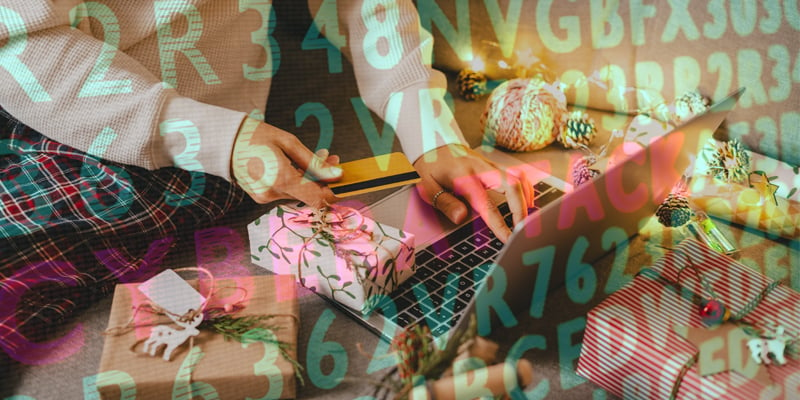
Preventative cybersecurity practices, especially during the holidays, — a time when online shopping undergoes a massive spike — are necessary. With increased financial and email activity, and considering intruders do not take holidays off, more chances arise for cyberattacks. With this frame of reference, a proactive approach that prevents information breaches and efficaciously protects your business is of great consequence.
What is Cybersecurity?
It is any strategy used to safeguard a company’s hardware, software, and data from security risks. Its goal is to have a detailed incident response plan for every possible emergency scenario in order to detect, contain, and eradicate threats, minimizing damages from malicious data breaches.
An important part of cybersecurity is risk assessment, which helps identify vulnerabilities in the IT systems that cybercriminals might be able to exploit. A comprehensive threat evaluation, detection, and prevention at every level of the organization is key to avoid future issues.
Damage to businesses
The Cybersecurity and Infrastructure Security Agency (CISA) has issued warnings in the past regarding cybersecurity risks during the holidays. They observed an increase in attacks occurring during a time when most people are off from work. Threat actors understand that holidays are a prime time for an attack, considering that:
- Businesses are closed during the holidays OR are operating with limited staff and resources.
- It is more common to find unsupervised IT networks and systems during the holidays.
- Employees are also more likely to become distracted or drop their guard as the festive spirit kicks in.
The damage a cyberattack can cause to a business could be disastrous. Stealing of personal or financial information, worsening of existing supply chain problems, threatening of stock availability, exorbitant ransomware demands, and irreparable harm to brand reputation and financial performance are just a few of the serious effects. Couple the above disruptions with the holiday season, and you are looking at devastation beyond what most organizations can fathom.
A dangerous vulnerability
Security systems, when not properly managed and integrated, might be accessed by hackers to get into an organization’s network. This can be a serious vulnerability, as cloud software is becoming more widely adopted across industries. Nevertheless, cloud integration can be more secure than legacy systems, if abundant safety protocols are applied, in which case cybersecurity and integrity can be exceptionally enhanced.
Cloud video surveillance and access control are at the top of the technologies businesses are implementing, due to their ease of use, remote capabilities, and cheaper costs. A best practice to avert potential cyberattacks when using the cloud is to change the default usernames and passwords of cameras, and other security devices, upon installation, and periodically after that. Strong passwords are a vital tool against harmful data breaches.
There are also concerns regarding the Internet of Things, as sensors can be used to access a network. Therefore, it is important that all device communications are secured with back-end systems. This can improve cybersecurity, even if there are lost or stolen devices.
In addition, Security 101 recommends:
There are several effective cybersecurity strategies that could greatly prevent attacks from hackers:
- Identify network weaknesses and vulnerabilities in connected devices.
- Share data security policies with your staff.
- Keep all software up to date.
- Older technologies can represent a cybersecurity risk. Consider the lifecycle of a product, proper operation, and regular maintenance to ensure your business stays secure.
- Add extra security to your organization’s email accounts.
- Human errors cause a significant amount of security breaches. Therefore, educating employees about how to recognize a phishing scheme is vital.
- Have a contingency plan.
In addition, since remote work environments seem to be the new normal, have employees address the security of their home networks. Personal computers are an easy way for attackers to gain access to networks. Ensuring employees have strong passwords to home routers and the proper firewalls lowers the chances of an attack.
As the holiday season is rapidly approaching, businesses should consider if their security strategy includes an effective plan for cyberattacks and the protection of data.
